In this tutorial we will go through the steps that need to be followed in order to implement LDAP(s) Microsoft Active Directory on Brocade SAN switches.
Authenticating with a local user on any network devices is not only time consuming, but also very dangerous in terms of security.
Before making any changes to your infrastructure, it is always recommended to make a copy of your switch configuration. Always make sure to perform changes onto testing devices before replicating them to your production environment.
On Fabric OS we have the possibility to use LDAP or LDAPS. As you can tell by its name, LDAP is the simple & unsecure protocol, and LDAPS uses certificates to perform the secure authentication.
Table of Contents
Certificate for LDAPs service
- Log in to your switch using an priviledged account
- To list the available certificate on the switch, use the command:
seccertmgmt show --all
- To create the Certificate Signing Request (.csr) use:
seccertmgmt generate -csr ldap
- Note the file name created in the previous step. File should end with .csr extension.
- To export the CSR file from the switch use the following command. Make sure to have any FTP client ready for transfer.
seccertmgmt export -csr ldap -protocol ftp
- Have the CSR file signed by your certificate administrator.
- First, we will import the CA (root & intermediate) bundled certificate.
seccertmgmt import -ca -client ldap
- If you don’t know how to combine root & intermediate CA certificate, please check Enable HTTPS protocol on Brocade switches under Combining Root and Intermediate certificate.
- Next, we will import the bundled certificate again, under server role. Use the same file as on step 6.
seccertmgmt import -ca -server ldap
- Finally, we will import the switch/client certificate that we exported in the previous step, and which should be signed by our certificate administrator.
seccertmgmt import -cert ldap
- At this point, we have completed LDAP certificates, we can continue with implementation.
Switch authentication methods
There are several methods to authenticate on the switch but we will make use of two. We will use LDAPS as primary authentication and Local DB as secondary. The secondary authentication comes in force if LDAP does not respond or if a local account & password is matched.
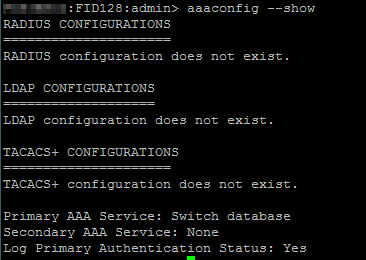
To see the current configuration use:
aaaconfig --show
To add an LDAP server to the switch use the following command:
aaaconfig --add <LDAP server FQDN> -conf ldap -d <domain name>
Where <LDAP server FQDN> is the Fully Qualified Domain Name of the LDAP server, for example ldap1.storcom.com
Where <domain name> is the domain name where the LDAP server resides in.
Finally, we will configure LDAP as primary authentication method, and local database as secondary:
aaaconfig --authspec "ldap;local"
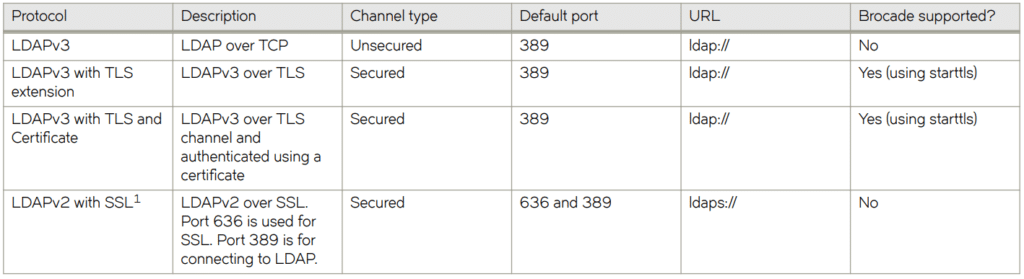
LDAP supported configurations
In the picture below we see different authentication configurations. In this tutorial we will use Option 3: LDAPv3 with TLS and Certificate over port 389
LDAPS implementation
Prior to performing any other configuration, we will have to create authentication groups in LDAP, or Active Directory in our case. Make sure to create the desired groups in AD so that we can make the link between them and the switch configuration.
In this example I have created an AD group called “STORCOM FOS Admins”. This LDAP group will be mapped against the local admin role on the switch.
To map the LDAP group with the SAN switch role, use the following command:
ldapcfg --maprole "STORCOM FOS Admins" admin
To add extra attributes, for example domain ID’s, use the following command:
ldapcfg -- mapattr "STORCOM FOS Admins" -l "admin=1-128" -h 128 -c admin
For more available attributes, please check Brocade Fabric OS Command Reference.
To see the existing role mappings, use:
ldapcfg --show
To unmap a role, use:
ldapcfg --unmaprole "STORCOM FOS Admins" admin
Any suggestion or question? Leave a reply below, or feel free to contact us. Also make sure to subscribe to our mailing list to get the latest updates.


One Response
Do you have any article for configuring secure syslog on brocade switch?