On Fabric OS we have the possibility to use LDAP
It’s obvious that more and more companies start investing on
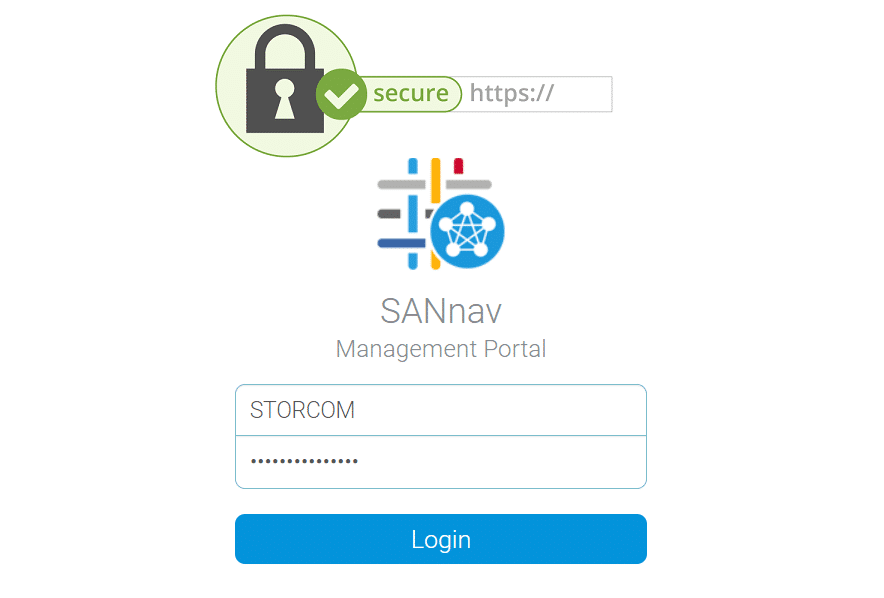
SANnav Management Portal utilizes by default a self-signed certificate, which
This article will focus on the implementation of the prerequisites
Secure communication over https is becoming mandatory for most of

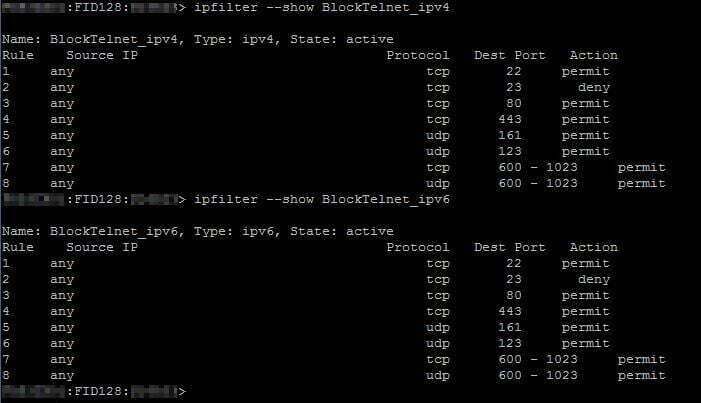
One of the most interesting parts of administrating FC switches
STORCOM BV is a registered company operating under the Belgian law. Our main activity is IT Consultancy.
Registered Office: Apollostraat 175, 2600 Antwerp [BE]
VAT: BE 0721.881.423 | Bank: BE50 7340 6436 0418
Tel: +32 (0) 486 71 21 41 | Email: contact@storcom.com