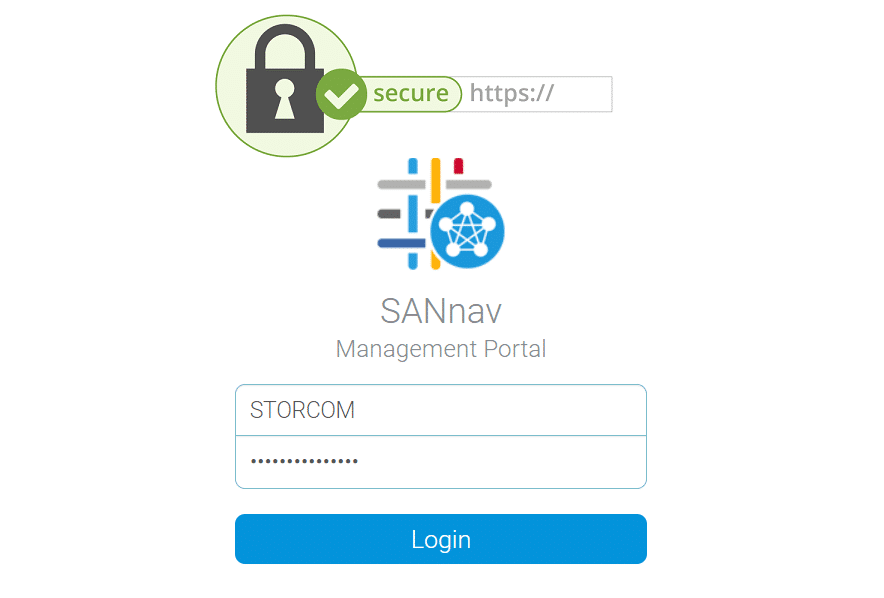
SANnav: Installing CA signed SSL certificate
SANnav Management Portal utilizes by default a self-signed certificate, which
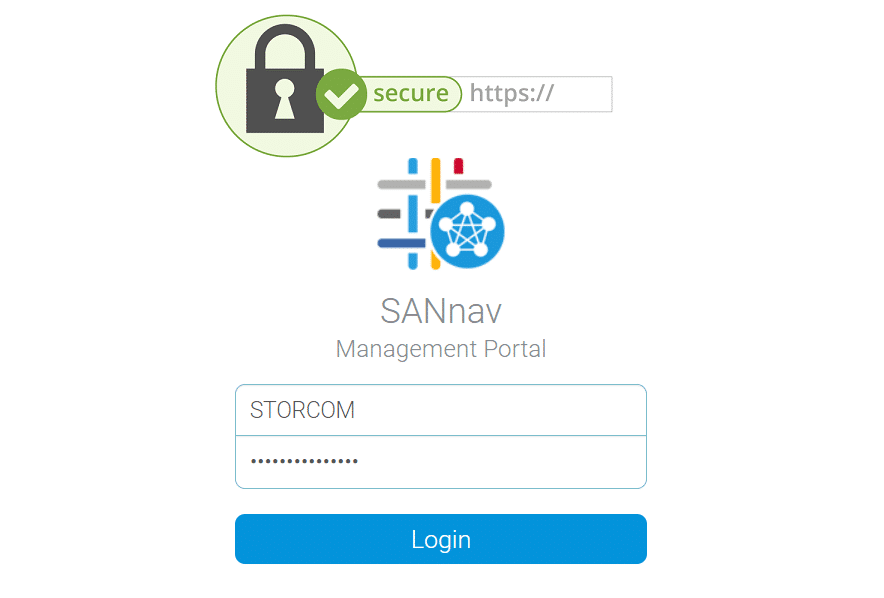
SANnav Management Portal utilizes by default a self-signed certificate, which
This article will focus on the implementation of the prerequisites
STORCOM BV is a registered company operating under the Belgian law. Our main activity is IT Consultancy.
Registered Office: Apollostraat 175, 2600 Antwerp [BE]
VAT: BE 0721.881.423 | Bank: BE50 7340 6436 0418
Tel: +32 (0) 486 71 21 41 | Email: contact@storcom.com